Installer Compromised
We have a cloud instance of SC. The group that set it up is no longer at the company. We have encountered several things that are concerning and if we do reach out to ConnectWise, gets some level 1, "check out this link" response and have yet to get an answer to any security related inquiry that was helpful.
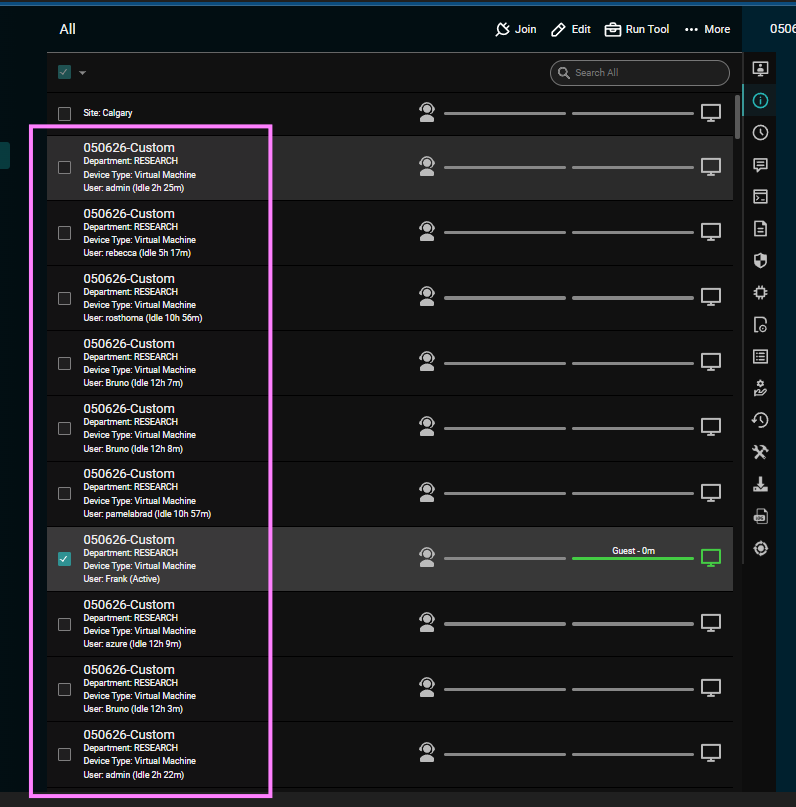
Currently, using the "Build+" option in the SC Access portal, create an installer package, and choose "Download"> > > within a couple of hours, a bunch devices that do not belong to us, show up in our access portal and we can utilize our full set of features on these unknown Japanese and Russian devices, where some screenshots seem to indicate we are looking at TA infra.
The newly downloaded exe and msi get flagged for numerous hits, not RMM tool hits but Malware and Trojan hits...if I run older exe' through the same analyzer, clean.


This is normal and has been going on for years across various remote monitoring and remote-control agents. This occurs when an AV or persistent threat utility uploads your binary and run them in sandboxes for a few moments to see if they are malicious or if they are doing anything malicious.